Importance of Security in Open-source Projects
Open-source software offers many great benefits, but it can be vulnerable to security flaws. Therefore, ensuring strong security protects your valuable data. Consequently, this practice maintains overall system reliability. In fact, a report by Synopsys revealed that over 84% of open-source codebases contain at least one known vulnerability. To address these risks, you should focus on several key areas, such as:
Key Focus Areas
- Data Protection: You must encrypt sensitive information to prevent unauthorized access.
- Code Review: A careful inspection of code helps teams identify potential vulnerabilities early.
- Standards Compliance: Following security best practices successfully reduces your digital risks.
Managing Security Updates
Regular updates for open-source software are truly essential. For instance, they actively prevent exploitation and dangerous cyberattacks. Moreover, data from Veracode shows that applying patches quickly can reduce the window of attack by up to 300%. Thus, taking proactive steps is vital. To achieve this, you can follow these effective steps:
Effective Steps
- Install Updates Promptly: This simple action reduces your direct exposure to known vulnerabilities.
- Track Versions: Monitoring small changes ensures your system remains completely stable.
- Test Before Deployment: You should verify updates first to avoid unexpected technical issues.
Managing Security Updates
Regular updates for open-source software are truly essential. For instance, they actively prevent exploitation and dangerous cyberattacks. Moreover, data from Veracode shows that applying patches quickly can reduce the window of attack by up to 300%. Thus, taking proactive steps is vital. To achieve this, you can follow these effective steps:
Effective Steps
- Install Updates Promptly: This simple action reduces your direct exposure to known vulnerabilities.
- Track Versions: Monitoring small changes ensures your system remains completely stable.
- Test Before Deployment: You should verify updates first to avoid unexpected technical issues.
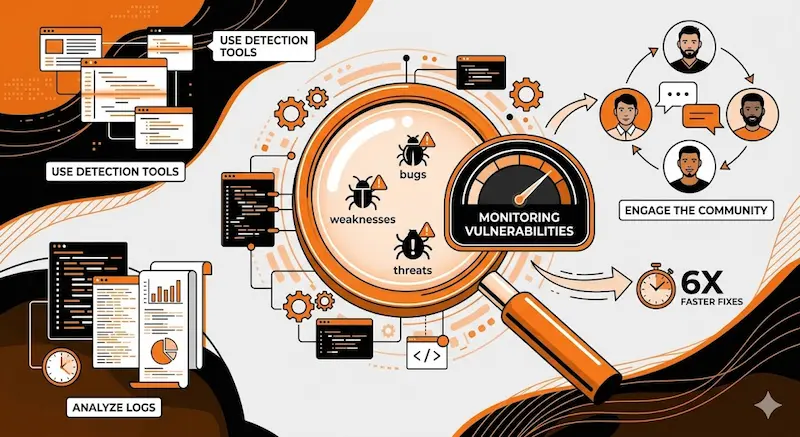
Monitoring Vulnerabilities and Threats
Early detection of security flaws successfully protects projects from sudden attacks. Furthermore, continuous monitoring is highly critical for every project. As a result, the GitHub Octoverse report highlights that automated security alerts help developers fix vulnerabilities up to 6 times faster. Therefore, you should adopt these monitoring strategies:
Monitoring Strategies
- Use Detection Tools: Automated programs identify hidden weaknesses very quickly.
- Analyze Logs: Tracking system activity easily reveals suspicious online behavior.
- Engage the Community: Sharing helpful information with developers accelerates the discovery of flaws.
Managing User Permissions
Controlling access rights successfully limits opportunities for exploits. In addition, it ensures total system integrity. However, many teams overlook this simple practice. Therefore, managing user permissions should be a top priority. To control this effectively, you can use these methods:
Control Methods
- Define Levels: You should grant permissions based solely on role and necessity.
- Regular Reviews: Periodic checks effectively prevent the accumulation of security risks.
- Strong Password Policies: This basic step protects accounts from unauthorized access.
Incident Response Planning
Proactive incident response minimizes the impact of attacks. Consequently, it reduces your potential financial losses. In fact, an IBM study found that companies with a tested response plan save an average of $2.66 million per breach. For this reason, preparation is highly valuable. To build a great plan, follow these response steps:
Response Steps
- Establish Clear Procedures: Define smart actions for handling security breaches.
- Immediate Reporting: Alert teams and users quickly to reduce further damage.
- Post-incident Analysis: Learning from small incidents effectively prevents future occurrences.